
MD5 Generator
A tool for creating an MD5 hash from a string. Use this fast, free tool to create an MD5 hash from a string.
In the ever-evolving world of cybersecurity and data integrity, MD5 generators stand as stalwart protectors of information. These cryptographic tools play a crucial role in verifying data integrity and ensuring the authenticity of digital assets. In this comprehensive guide, we'll delve into the world of MD5 generators, explaining what they are, how they work, and why they are indispensable in today's digital landscape.
What is MD5?
MD5, short for Message Digest Algorithm 5, is a widely-used cryptographic hash function. It takes an input (or 'message') and produces a fixed-size, 128-bit hash value. This value, known as the MD5 hash, is a unique representation of the input data. Even the slightest change in the input data will result in a significantly different MD5 hash.
How MD5 Generators Work
MD5 generators work by applying a series of complex mathematical operations to the input data. These operations create a unique fingerprint for the data, which is nearly impossible to reverse-engineer. MD5 generators are deterministic, meaning the same input will always produce the same MD5 hash.
How can you use this tool?
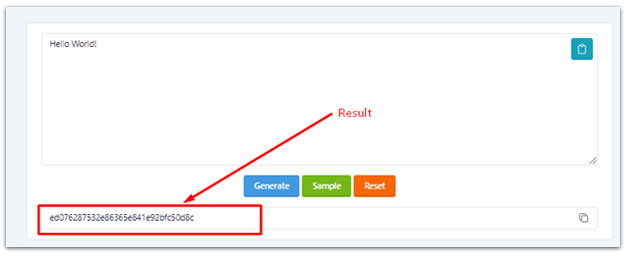
When you need to convert text to md5 format then this tool will help you. In the beginning of clicking the tool you will see the picture below.
In the tool you will find some options like paste, generate, sample, reset.
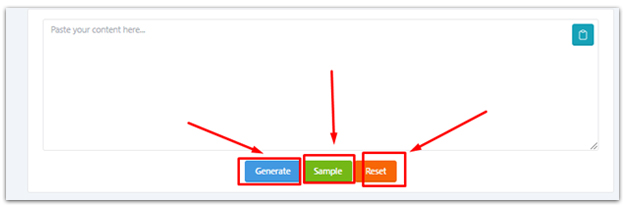
When you click the sample button a pre saved text will automatically paste in the tool's text type area. You can clear the text area by clicking the reset button.
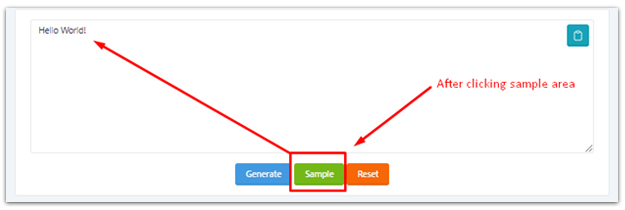
Write your desired text in the text box. Be careful during typing. You can easily paste your text from your clipboard with just one click.

Now it is time to generate your md5 format. For this just click the generate button.
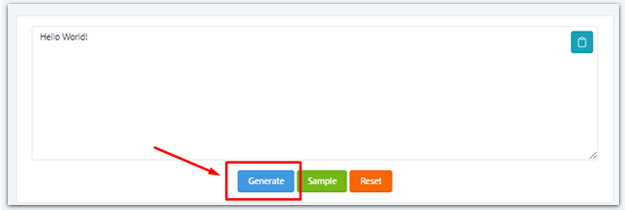
The result will show below just like this. You can easily copy this with just one click with the copy icon.
We think you can easily use this tool. Just follow the user manual. Further if you have any problem or question you can contact us. We will help you as soon as possible.
Use Cases of MD5 Generators
MD5 generators are commonly used to check the integrity of files and data during transmission. By comparing the MD5 hash of the received data with the original hash, users can quickly detect any alterations or corruption. In the realm of cybersecurity, MD5 hashes are employed to store passwords securely. Instead of storing the actual password, websites and systems store the MD5 hash of the password. This way, even if the database is compromised, the hacker cannot easily recover the original passwords.
In Digital Signatures and Forensics Investigations
MD5 generators are integral in creating digital signatures for documents and software. By hashing the contents and encrypting the hash value with a private key, digital signatures verify the authenticity of the sender and the integrity of the message. In the world of digital forensics, MD5 hashes are used to verify the integrity of evidence. Investigators can compare MD5 hashes of files to ensure they have not been tampered with during the investigation.
The Controversy Surrounding MD5
While MD5 generators have been widely used for decades, they are not without controversy. Advances in computing power have made it possible to find collisions (different inputs that produce the same MD5 hash) and vulnerabilities in the algorithm. As a result, MD5 is considered deprecated for certain security-critical applications.
Conclusion
MD5 generators play a vital role in ensuring data integrity, password security, and digital signatures. While they are no longer suitable for the most security-sensitive applications, they remain valuable tools in various contexts. Understanding how MD5 generators work and their applications is essential for anyone navigating the complex landscape of digital security and data integrity. In an era where data breaches and cyber threats are commonplace, MD5 generators serve as a testament to the ongoing battle to secure our digital world. Whether used for verifying the authenticity of files or enhancing the security of digital communications, MD5 generators continue to be a valuable asset in the toolkit of IT professionals and cybersecurity experts.











